A VPN is no longer just a tool for hiding your IP address or streaming content from another region. For businesses, developers, remote teams, and privacy-focused users, a VPN has become a practical part of day-to-day security. If you want more control, stronger privacy, and better performance, one of the smartest options is to set up a VPN on dedicated server.
A self-hosted VPN gives you something a shared VPN service cannot always offer: ownership. You control the server, the software, the access, and the data flow. That means fewer unknowns, more flexibility, and a more stable environment for secure communication.
In this guide, you will learn how to set up a VPN on dedicated server in a simple and readable way. We will cover what a dedicated server VPN is, why people use it, what you need before you start, the best VPN protocols to consider, the setup process, and the security steps that matter most.
What Does It Mean to Set Up a VPN on Dedicated Server?
When you set up a VPN on a dedicated server, you put VPN software on a physical server that is only yours. That server becomes the safe link between your device and the internet or between your team and internal resources.
Instead of relying on a third-party commercial VPN provider, you build your own VPN endpoint. Once connected, your internet traffic or internal traffic is encrypted and routed through that server.
This kind of setup is often used for:
- secure remote work access
- private business communication
- encrypted browsing on public Wi-Fi
- safe access to internal applications
- connecting multiple offices or team members
- protecting sensitive data transfers
Why Use a Dedicated Server for a VPN?
You can technically host a VPN on a VPS, cloud instance, or even a home machine. But a dedicated server offers clear advantages when security, performance, and reliability matter.
Better Performance
A dedicated server gives you exclusive access to the machine’s CPU, RAM, storage, and network resources. Since there are no neighboring users consuming those resources, your VPN can perform more consistently. This matters when multiple users connect at the same time or when you transfer large files over the VPN.
More Privacy and Control
With a dedicated server, you are not depending on a consumer VPN company to manage your environment. You control the software stack, authentication method, access logs, and firewall rules. For many businesses, that level of control is a major benefit.
Stable Connections
A private VPN server on dedicated hosting can provide more stable connectivity for remote teams, developers, and admins who need regular secure access. Compared to home-hosted VPNs, a professionally hosted dedicated server usually has better uptime and bandwidth.
Custom Security Rules
A self-hosted VPN server allows you to configure exactly how users connect, what ports are open, which devices are allowed, and how traffic is routed. This is ideal for businesses with specific compliance or access needs.
Dedicated Server VPN Use Cases
A VPN on dedicated server is not just for large companies. It fits many real-world needs.
Remote Team Access
If your employees need to access internal dashboards, databases, or private files, a VPN gives them a secure path without exposing everything directly to the public internet.
Secure Admin Access
System administrators often use a VPN to reach hosting panels, SSH services, or internal management tools safely from different locations.
Privacy-Focused Browsing
Some users want their internet traffic encrypted without trusting public VPN brands. A self-hosted VPN can be a clean solution for private browsing, especially on public networks.
Site-to-Site Communication
Businesses with more than one office or infrastructure location can use a VPN to connect systems securely over the internet.
Safe Development and Testing
Developers can use a private VPN server to test applications in a secure environment or to restrict staging access to approved team members only.

What You Need Before You Start
Before you set up a VPN on dedicated server, make sure you have a few basics in place.
- A Dedicated Server
You need a dedicated server with root or full administrator access. Linux is the most common choice because it is stable, efficient, and widely supported by VPN tools. - A Clean Operating System
Ubuntu, Debian, and CentOS are commonly used for VPN installations. Ubuntu is a popular choice because documentation is widely available and setup is usually straightforward. - A Static Public IP Address
Your VPN clients need a fixed address to connect to. Most dedicated servers come with a static public IP by default. - Basic Command Line Access
Most VPN setups are done over SSH. You do not need to be an expert, but you should be comfortable copying commands and editing configuration files. - Firewall Access
You must be able to open the required VPN ports in your server firewall or hosting firewall.
Choosing the Right VPN Protocol
For a WireGuard VPN server, install the WireGuard package and related tools.
For OpenVPN, install the OpenVPN package and any certificate management tools required.
Many admins prefer WireGuard because its setup is lighter and easier to understand. OpenVPN can take more time because it usually involves certificates, keys, and more layered configuration.
WireGuard
WireGuard is modern, lightweight, and fast. It is known for simple configuration and excellent performance. Many users now prefer WireGuard for a secure VPN setup because it is easy to maintain and often faster than older protocols.
- fast and efficient
- modern cryptography
- simpler configuration
- lower system overhead
- good for mobile and desktop clients
OpenVPN
OpenVPN has been around for years and remains a trusted option. It is flexible, widely supported, and works well in many network environments.
- mature and battle-tested
- highly configurable
- broad client support
- useful in restrictive network conditions
If you want a simple and high-performance dedicated server VPN, WireGuard is often the first choice. If you need broader legacy compatibility or advanced customization, OpenVPN still makes sense.
Step-by-Step: How to Set Up a VPN on Dedicated Server
Let’s walk through the setup in a practical way. The exact commands can vary depending on your operating system and VPN protocol, but the overall process stays similar.
Step 1: Update the Server
Before installing anything, make sure your server is updated. This reduces the chance of software conflicts and improves security.
You should:
- update package lists
- upgrade installed packages
- reboot the server if needed
A clean, updated server gives you a better foundation for a stable VPN on dedicated server.
Step 2: Choose and Install the VPN Software
At this stage, decide whether you want WireGuard or OpenVPN.
For a WireGuard VPN server, install the WireGuard package and related tools. For OpenVPN, install the OpenVPN package and any certificate management tools required.
Many admins prefer WireGuard because its setup is lighter and easier to understand. OpenVPN can take more time because it usually involves certificates, keys, and more layered configuration.
Step 3: Generate Server Keys and Client Credentials
Every secure VPN setup depends on authentication.
For WireGuard:
- generate a private key for the server
- generate a public key from it
- create keys for each client device
For OpenVPN:
- create a certificate authority
- generate server certificates
- create unique client certificates
The purpose here is simple: only trusted devices should be able to connect.
Step 4: Configure the VPN Interface
The VPN software needs a virtual network interface. This is where internal VPN traffic flows.
You will define:
- the VPN subnet
- server IP inside the tunnel
- listening port
- encryption details
- DNS settings
- Peer or client definitions.
Step 5: Enable IP Forwarding
If you want client devices to access the internet through the VPN or reach other networks behind the server, IP forwarding must be enabled.
This tells the server to pass traffic between interfaces instead of dropping it. Without this step, your VPN may connect successfully but still fail to route traffic correctly.
Step 6: Set Up Firewall and NAT Rules
A dedicated server VPN needs firewall rules that allow incoming VPN traffic and network address translation rules that route client traffic properly.
Typical tasks include:
- allowing the VPN port
- permitting tunnel traffic
- enabling forwarding rules
- applying NAT so client requests can reach the internet
This is one of the most important parts of the setup. A missing firewall rule is one of the most common reasons a VPN connection fails even when the installation looks correct.
Step 7: Start and Enable the VPN Service
Once the configuration is in place, start the VPN service and enable it to launch automatically after reboot.
This makes sure your private VPN server stays available even after maintenance or a system restart.
Always verify that the service is running cleanly and that there are no configuration errors in the service logs.
Step 8: Create Client Profiles
Now it is time to configure the devices that will connect to your VPN.
This may include:
- laptops
- mobile phones
- desktops
- routers
- remote office systems
For each client, create a profile or configuration file. Import it into the WireGuard or OpenVPN app on the device. Then connect and test whether:
- the tunnel comes up
- traffic is encrypted
- DNS works
- the correct routes are applied
Step 9: Test the Connection
A proper test is not just “it connected.” You should check the full behavior of the VPN.
Test:
- whether the client gets a VPN IP
- whether internet traffic works through the tunnel
- whether you can reach private services
- whether DNS requests resolve correctly
- whether the public IP changes to the server IP if full tunnel mode is enabled
This step helps you spot routing or firewall mistakes early.
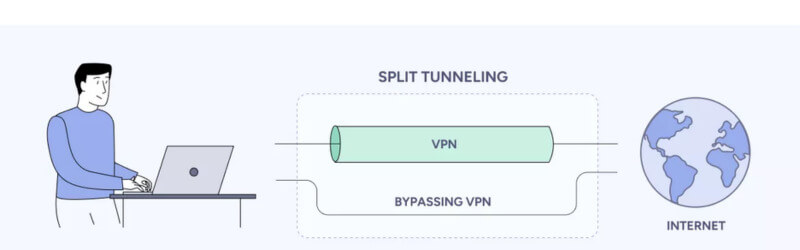
Full Tunnel vs Split Tunnel
When building a self-hosted VPN server, you should decide how traffic will flow.
Full Tunnel
In a full tunnel setup, all client internet traffic passes through the VPN server. This gives stronger privacy and makes sense when users need secure browsing on public networks.
Benefits:
- all traffic is encrypted
- better privacy on public Wi-Fi
- consistent network path
Drawbacks:
- more load on the server
- may add some latency
- all bandwidth usage passes through the VPN
Split Tunnel
In a split tunnel setup, only traffic meant for private resources goes through the VPN. Normal internet browsing goes out directly through the user’s own connection.
Benefits:
- lower server load
- better speed for general browsing
- efficient for remote work access
Drawbacks:
- less privacy for non-VPN traffic
- more careful route planning needed
For business access, split tunneling is often enough. For privacy-focused usage, full tunneling is more common.
How to Secure Your VPN Server Properly
Setting up a VPN is only half the job. Securing it is what makes it valuable.
Use Strong Authentication
Do not reuse credentials. Use unique keys, certificates, or strong passwords. If possible, add multi-factor authentication for admin access to the server itself.
Change Default Ports Carefully
Limit SSH Access
If your VPN server runs on Linux, secure SSH properly:
- mdisable password login if possible
- muse SSH keys
- mlimit allowed users
- mchange the default SSH port if needed
- install fail2ban or similar protection
Keep the Server Updated
An outdated server is an easy target. Patch the operating system, the VPN software, and related packages regularly.
Monitor Logs
Check authentication logs, connection attempts, and service logs. This helps you notice failed login patterns, unusual activity, or configuration problems early.
Restrict Access by IP When Possible
If only certain offices or admins need access, allow connections only from specific IP ranges where practical.
Use a Strong Firewall Policy
Open only the ports you need. Everything else should remain closed.
Common Problems During VPN Setup
Even a well-planned VPN on dedicated server can run into a few common issues.
Connection Times Out
This usually means:
- the VPN port is blocked
- the service is not running
- the firewall is misconfigured
- the client is pointing to the wrong IP
Connected But No Internet
This often happens when:
- IP forwarding is disabled
- NAT rules are missing
- DNS is not configured properly
Client Cannot Reach Internal Services
Possible reasons include:
- wrong routing rules
- overlapping subnets
- firewall restrictions on the internal services
Slow Speed
A dedicated server VPN is usually stable, but speed can still be affected by:
- encryption overhead
- distance between user and server
- server network quality
- wrong MTU settings
- overloaded routes
WireGuard vs OpenVPN: Which Is Better for a Dedicated Server?
There is no universal answer, but for most new deployments, WireGuard is the simpler and faster option.
Choose WireGuard if you want:
- easier setup
- excellent speed
- modern security
- lower resource usage
Choose OpenVPN if you want:
- traditional enterprise familiarity
- more mature documentation in older environments
- compatibility with legacy workflows
- advanced connection flexibility
For most modern use cases, a WireGuard VPN server on dedicated hosting is a strong pick.
Best Practices for Running a Private VPN Server Long Term
Once your VPN is live, keep it clean and manageable.
Document Your Setup
Write down:
- server IP
- port numbers
- client names
- internal VPN subnet
- key rotation dates
- firewall rules
This saves time during troubleshooting.
Remove Unused Clients
If an employee leaves or a device is lost, revoke access immediately.
Rotate Keys Periodically
Key rotation improves security, especially for business environments.
Back Up Configuration Files
Store encrypted backups of your VPN config, keys, and setup notes in a safe place.
Watch Bandwidth Usage
If multiple users rely on the VPN every day, track traffic and server load so performance remains stable.
Is a Self-Hosted VPN Better Than a Commercial VPN?
It depends on your goal.
A commercial VPN is easier if you just want a quick service with minimal setup. But a self-hosted VPN server gives you more control and can be a better fit for secure business access, remote administration, and private team communication.
A dedicated server VPN is especially useful when:
- you want full ownership
- you need predictable performance
- you want to secure internal business resources
- you do not want to rely fully on third-party logging policies
- you want to control who has access and how they connect
For many businesses and advanced users, that extra control is worth it.
Conclusion
Setting up a VPN on a dedicated server may seem hard at first, but with the right setup, it can be a useful and powerful security tool. A dedicated server gives you better control, privacy, and stable performance for safe access, whether you choose WireGuard for speed or OpenVPN for flexibility.